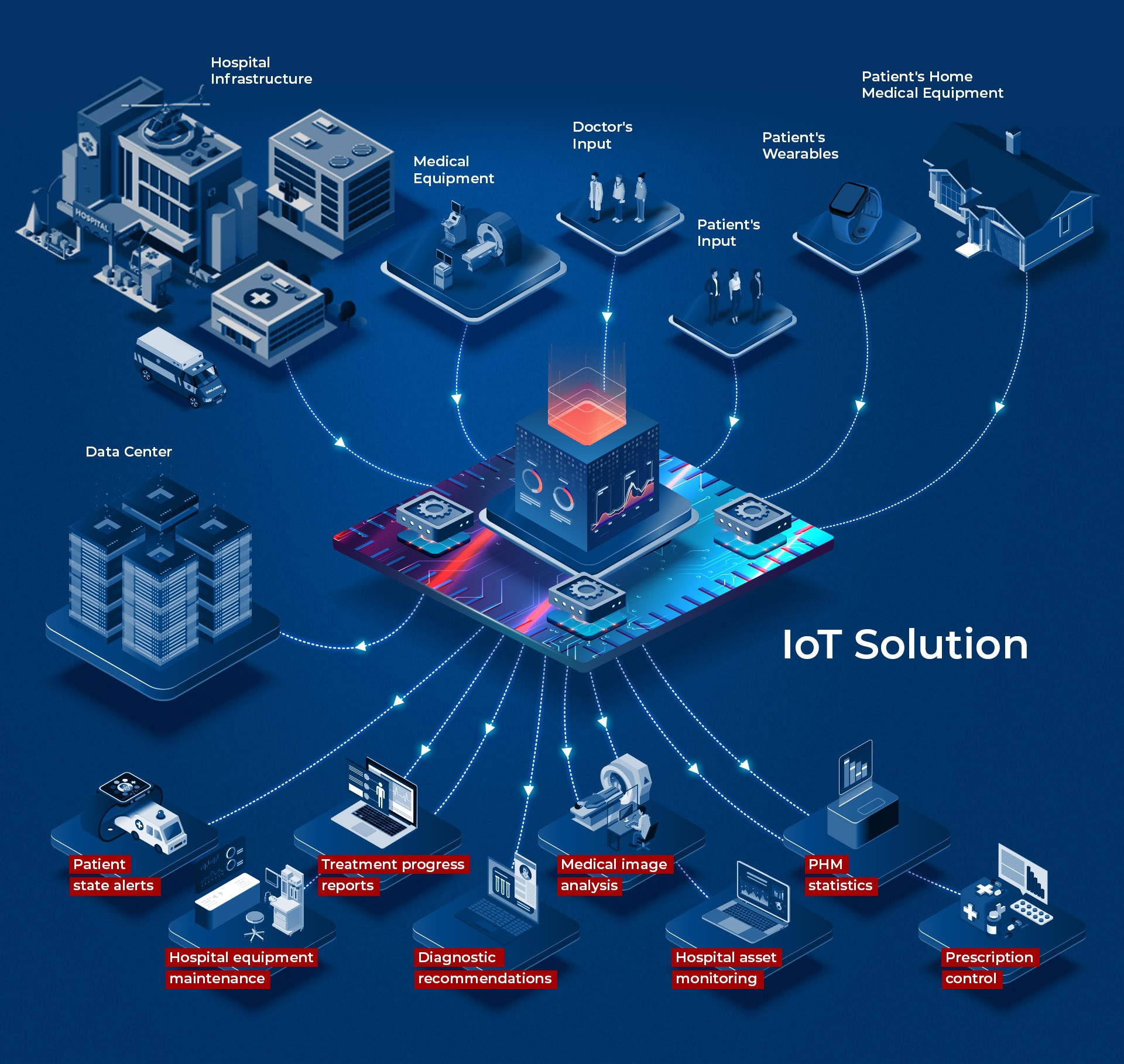
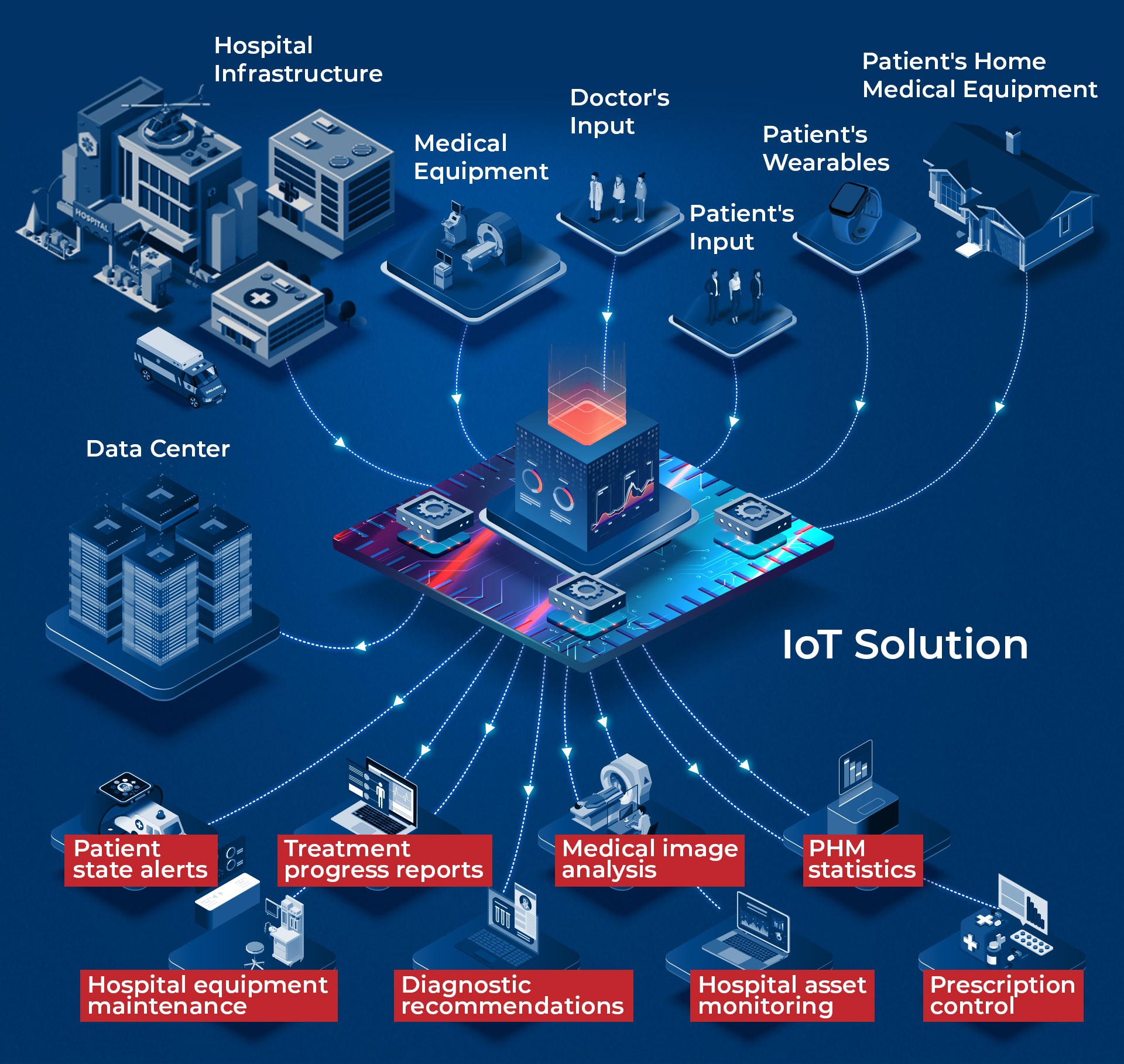
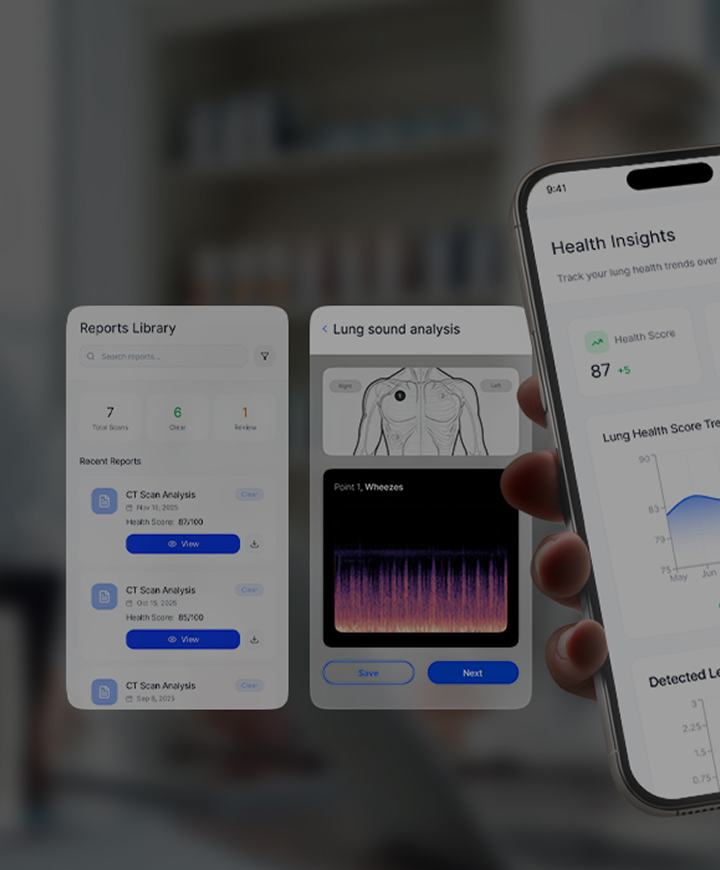
Health data collection and analytics
Quickly and efficiently, collect more health-related data than ever before to enrich the health profiles of your patients. Apply sophisticated tools to process the information and generate deep insights into health outcomes on individual or population level.
- Fast and easy health data exchange
- Large-scale data collection via web, mobile, consumer wearables, and medical devices
- Data-driven diagnostics, including CV-assisted medical imaging
- Inpatient monitoring (smart BP cuffs, glucometers, holters, etc.)
- Remote patient monitoring (RPM)
- IoT solutions for population health management (PHM)
- Patient-generated data solutions and mHealth apps (Google Fit, Apple HealthKit)